Chasing an active Social Engineering Fraud at Amazon Kindle
TL;DR: I've just spent several hours chasing a socially engineered (not password compromised) stolen Kindle through a series of phone calls, chats, virtual shipping addresses, UPS tracking numbers and more. The irony is that my wasted time is the real loss.
NOTE: Amazon Kindle Support is, and continues to be truly amazing. However, in this instance, they have flawed policies that I have no doubt will be fixed.
All this for the want of a $119 Kindle. Let me start over.
Yesterday I got an email from Amazon that said:
I'm writing to follow-up on our recent chat conversation.
I'm sorry to hear about the problem with your Kindle. I'm sending you a replacement Kindle via Two-Day shipping to get it to you as soon as possible.
...
Guaranteed Delivery Date: Tuesday, February 12, 2013.
Hm? What? Is this a Phish? No, all the links are valid, email return path is correct, and I confirmed I've received emails like this before.
I log into my Amazon account and I see:
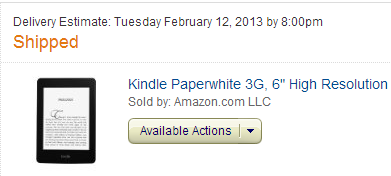
Holy crap. I didn't order that. I click Cancel. Then I get this email a few minutes later:
We weren't able to cancel the following item(s) from your order:
Kindle Paperwhite 3G, 6" High Resolution Display with Built-in Light, Free 3G + Wi-Fi
Looks like they are so efficient that they got the Kindle on the truck already. I check UPS. It's on the way to my house.
I login to Amazon's "Manage Your Kindle" page, and sure enough, there's already 'Scott's 2nd Kindle' sitting there, ready to go. I deregister it.
Hm? Why is this useful? Why do they want a Kindle sent to my house?
At this point I call Amazon and explain the situation to a human. Sue is SUPER nice, SUPER knowledgeable and immediately I can tell she gets it, so someone give Sue G. a raise. She says she's taking it to Fraud and I should hear from them soon. I want to point out here that I'm talking to a human on the phone here.
Sue looks through their details and says there are a series of chats with "Scott" using their Live Chat system. So, this is a social engineering hack, not a "password compromised" hack. The person has reported that "Scott's" Kindle is broken and has asked for a replacement, but then later tried to redirect the delivery. The customer rep says they can't redirect it. However, it appears the bad guy tried multiple support folks until they finally got the package redirected. More on that in a second.
Note that none of this required anything more than my address and my email. They were able to get the Amazon Customer Service to accept that they were me without my password or any additional verification.
I ask Sue to send me the chat logs. She talks to a supervisor and says she can't send them to me because the chat logs contain the address that the bad guy wants to redirect to. She does tell me the redirect address is in Portland, however.
ASIDE: Amazon customer support also "brick" the Kindle for me. It's not just Deregistered (disassociated from my account) now, but it's remotely deactivated. However, I still don't want the bad guy to succeed.
Sue also mentions that the bad guy asked that the customer representative "not bother to send a follow up email, as I never check my email anyway." The bad guy is consistent in this behavior, always asking to avoid the return emails so I won't see them. Of course, the automated system can't NOT send the follow up, which is why we're here now. If that automated email hadn't gone out I wouldn't have noticed this hack until I checked my Amazon Recent Orders at some point in the future.
ASIDE: It's rather ironic that the bad guy's address has more privacy than I do.
RECOMMENDATION: I recommend that Amazon implement a policy wherein they email the complete customer chat transcripts after the chat completes. Additionally, my chat transcripts are mine and should be available to me online.
I figure it's done and I go about my day. Next morning I wake up to see a bunch of mails like this, all from different people at Amazon:
Thank you for contacting Amazon.com about your inquiry. It was a pleasure to help you with your concern.
I can confirm that we still expect to ship your order in time to be delivered to you by February 12th, 2013.
We'll send you an e-mail when your order is shipped with your tracking number. Your order could ship any time between now and right before the estimated delivery date.
Waa? What "concern?" I go to UPS and check the tracking number for the ill-gotten Kindle.
Note the times. Someone is doing this when Amazon phone support is overseas, or when they (the bad guy) is overseas, or at least, up late.
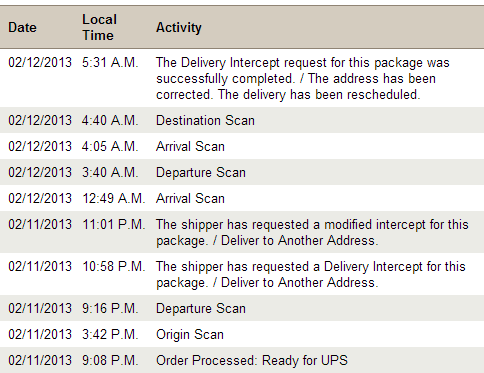
They are still trying to redirect the Kindle to another address, again with the web chat system and multiple times. This sure is a lot of work for a Kindle.
I call Amazon again and re-explain what's up. I ask for the chat transcripts again but they won't send them. Simultaneous to this phone call I email Amazon Customer Support and ask for the chat transcripts (via email, just to be clear) and the chat transcripts show up quickly in my inbox. Doh.
RECOMMENDATION: I'm reiterating here. Policies only work when everyone follows them. The phone folks at Amazon are very consistent, but the chat and email support is, in this case at least, demonstrably spotty.
NOTE: The bad guy isn't "ordering" new stuff, but rather requesting a replacement of an existing product exploiting Amazon's liberal warranty replacement service, then redirecting the package.
OK, now I've got chat transcripts. Here's the annotated and edited transcript.
In case it's not crystal clear here, that's not me chatting here.
Transfer Notes : May I check on my replacement Kindle shipment status that was placed earlier today?
10:11 PM Scott is off hold.
10:12 PM Scott : Hi [Name withheld]
10:12 PM Amazon Rep : Hello, Scott.
10:12 PM Amazon Rep : Could you please help me with the order number?
10:13 PM Scott : I do not have the order number with me right now. Could you please help look into my account? The order was placed earlier in the day.
(ED: Note to Amazon, this is odd, as they are sitting at a computer)
10:13 PM Amazon Rep : Scott, I need the email address associated with your amazon account?
10:13 PM Scott : sure.
10:13 PM Scott : [my email address]
10:14 PM Amazon Rep : Please give me a minute to check that.
10:15 PM Amazon Rep : Before I can view your account I'll need to do a quick security check. Please confirm the email address, complete name, and billing address on your account.
10:16 PM Scott : [my address]
10:16 PM Scott : scott hanselman
10:17 PM Amazon Rep : Thank you for the information.
10:19 PM Amazon Rep : The kindle device which your referring to will be delivered to you by: Tuesday, February 12, 2013
10:19 PM Scott : do you have the tracking number for this shipment?
10:20 PM Amazon Rep : Yes, the tracking number is 1Z0ERxxxxxxxxxxxx
10:23 PM Scott : Thank you.
10:23 PM Amazon Rep : You’re welcome!
10:24 PM Scott : Please hold on.
10:24 PM Amazon Rep : Sure.
10:25 PM Scott : May I know how can I change the shipping address?
10:25 PM Scott : I just contacted UPS, and was told to contact the shipper, which is Amazon, to change the shipping address.
10:25 PM Amazon Rep : This is the shipping address:
Scott Hanselman
[my address]
United States
(ED: Note that they included "United States." This tells me this was copy pasted. No one writes that.)
Primary Phone: [my phone]
10:26 PM Scott : Yes, but I would like to change the shipping address.
10:26 PM Amazon Rep : I am sorry, the shipping address cannot be changed now, since the item has been shipped.
10:27 PM Scott : I understand, but UPS told me that this is still possible, but only Amazon can contact UPS to do so.
10:27 PM Scott : Are you able to transfer me to someone who is able to help out?
10:27 PM Amazon Rep : Please give me a minute to check that.
10:29 PM Amazon Rep : Thank you for being on hold.
10:29 PM Amazon Rep : I've contacted UPS and asked them to hold this package for you.
10:29 PM Scott : ?
10:30 PM Scott : I do not need UPS to hold the package for me.
10:30 PM Scott : Please confirm with me first before making any changes.
10:30 PM Amazon Rep : I understand that you want to change the address, but that cannot be done now since the package has been shipped.
10:31 PM Scott : Could you please help me call UPS to enquire?
10:31 PM Amazon Rep : Sure.
10:32 PM Scott : If you are not able to make any outgoing calls, please transfer me to a colleague who may do so.
10:34 PM Amazon Rep : Please give me a minute to do that.
10:34 PM Scott : Sure.
10:35 PM Scott : http://www.ups.com/content/us/en/resources/service/delivery_change.html
10:41 PM Amazon Rep : Scott, could you please help me with the address to which you want the package to be redirected to?
10:41 PM Scott : Sure.
10:42 PM Scott : [Address in Portland with "NUM99999" at the end of the street]
(ED: This US address is a "Shipping Portal into another country. More on this soon.)
10:43 PM Amazon Rep : Thank you for the information.
10:43 PM Amazon Rep : Please be on hold while I contact UPS regarding it.
10:52 PM Amazon Rep : Thank you for being on hold.
10:52 PM Amazon Rep : Could you please help me with your phone number?
10:53 PM Scott : No worries.
10:53 PM Scott : Sure
10:53 PM Scott : 425-406-xxxx
(ED: I called this. It's a disconnected VOIP number)
10:53 PM Amazon Rep : Please give me a minute.
10:55 PM Amazon Rep : Could you please help me with your country code?
10:56 PM Amazon Rep : Thank you.
11:01 PM Amazon Rep : I am sorry for the delay.
11:01 PM Scott : No worries.
(ED: Conjecture: People comfortable with English say this. This isn't something you hear a lot of non-natives say.)
11:01 PM Amazon Rep : I have requested for a delivery change of the address to the UPS carrier.
11:02 PM Scott : Thank you. May I know when is the scheduled delivery date?
11:03 PM Amazon Rep : You're Welcome. Yes, it will be delivered as scheduled.
11:03 PM Amazon Rep : Here is the link, you may view the details:
http://wwwapps.ups.com/WebTracking/processInputRequest?
11:04 PM Scott : Thank you so much. You do not need to follow up with an email to me as I hardly check my emails. Would that be okay?
(ED: Seriously?)
11:05 PM Amazon Rep : You're Welcome. I am sorry, I'll need to send you an follow up email.
11:05 PM Scott : Oh. You do not have to do so actually.
11:06 PM Amazon Rep : I understand your concern, but as per our policy I'll need to send you an email.
11:06 PM Scott : An auto generated email to complete the survey is fine.
11:06 PM Amazon Rep : Okay, sure.
11:07 PM Scott : I will complete the survey when I have the time, but you don't have to include other details in the email.
(ED: Not cool, Amazon.)
11:07 PM Amazon Rep : Sure, Scott. I'll do that.
Amazon Fraud will handle the IP address tracking and deal with the bad guy, but now I have an address. I get a website and phone number from the address. It's a global shipping logistics company. The weird number at the end of their address is a Virtual Routing number.
An address with a number after it allows folks to have a package mailed to them in the US, then the package is transparently forwarded overseas. This number points to an account they have with a post office in a country in Southeast Asia. They received packages from all over, consolidate them, then ship them on masse. This allows governments and companies (and apparently bad guys) to order stuff from companies inside the US, then pay the international shipping and tariffs as a large shipment when it's sent overseas.
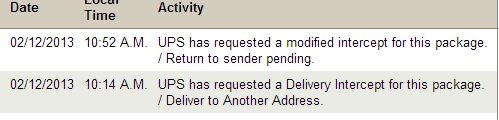
I call UPS with Amazon and we initiate an irreversible Return to Shipper. Amazon Fraud is on it, police contacted. This event is done.
UPDATE: Looks like the use of a Domestic Remailer company also hit Chris Cardinal. Someone tried to have a product mailed to an address in Portland, to a different "logistics company" that forwards mail overseas.
Buy why?
Why all this work for a Kindle? No rock solid idea. Perhaps:
- Practice? If they can do one they can do 10, then 100?
- Kindles, especially 3G Kindles, are preregistered to an account that may have One Click Ordering turned on.
- With a Kindle registered to me, someone might be able to use it to order a bunch of stuff before anyone is on to them. I've said before that a Kindle is "There's a single click between my Wallet and Jeff Bezo's Wallet." This is truer than ever in my mind now.
How does Amazon fix this?
Here's my recommendations to Amazon on how to fix this.
- The IP address that the chat happened from was clearly not mine, nor was it likely in my neighborhood.
- Amazon, like a bank, should notice if a chat or request happens from an unknown location and enforce secondary protocols to check identity.
- Everything was done over web chat without the user being logged in.
- No order change should EVER happen anonymously over web chat. Authenticate the user the way you already know how - by making them log in.
- The bad guy was saying clearly suspicious things. They asked the rep NOT to send emails. That behavior is not normal.
- Train customer service reps to watch for obviously sneaky behavior, and re-authenticate.
- The chat transcript wasn't emailed to me. I was notified about an interaction, but not given the context.
- All chat transcripts should be emailed to the account owner after they are concluded. Chat transcripts should be available to me from my account pages.
- A half dozen attempts were made in a short period.
- It appears that the customer reps didn't read the previous interactions and notice that this person was effectively phishing the reps themselves, trying to get satisfaction.
- The UPS shipping redirect was allowed without authorization.
- Changing where something is shipped is a big deal. It should be done with significant authentication in place.
- The resulting destination address was a known international logistics package distributor.
- There are three in Oregon, which means there are likely only a few hundred, maybe a thousand in the US. Scrutinize orders sent to these "mail launderers."
What do you think?
About Scott
Scott Hanselman is a former professor, former Chief Architect in finance, now speaker, consultant, father, diabetic, and Microsoft employee. He is a failed stand-up comic, a cornrower, and a book author.
About Newsletter
Thanks for taking the time to share this Scott.
Dennis
In Belgium, at a certain online travel agency, you can book a holiday for someone with just their name and address... Then they have to cancel it, and be find with cancellation costs that can be up to 80% of the price of the Holiday. If you want to really hurt someone financially. This stuff scares me, because all my "private" or what these companies consider private enough information is publicly available online.
What are the police going to do about this? Nothing.
1) Initially finding the "Contact Amazon" link was truly painly and unintuitive - like many major companies they try to provide automated options for most issues - but there are times when you really just need to speak to someone.
2) When I found the support link, it was awesome. They will dial your phone then and there, and a support consultant usually hooks up with the opened phone line almost immediately.
3) Simple one time queries are good - I didn't get the impression there was much flip chart action going on.
4) Non simple one time queries can be a nightmare - the staff don't seem to read the history - so if there are any sensitivities involved its best not to assume these are taken for granted. And if they can get it into the reorder/return item queue quickly they will.
5) Hooray for UPS! Here in the UK, Amazon items are dispatched by multiple delivery companies. So it can really become a postcode lottery. I ordered a DVD for someone who was out of the house during business hours - and the delivery company attempted to deliver to the same property 3 times even though I instructed Amazon to deliver elsewhere. After 3 goes, the item goes back to the warehouse. The comms between Amazon and the delivery companies isnt always the best - but a word with support can send the wrath of god down the supply chain.
6) Going back to point 5, I like impressing my non-IT acquaintances by being the red telephone. You need a birthday present in 5 days - just speak to Jim - he pushes buttons and the thing just arrives. But if your friend lives in the middle of the countryside - and the van drivers are grumpy, the delivery item can suddenly develop an unwanted vulnerability around it - and you can lose hours of your day to stress and contacting Amazon support - even though they may not be directly to blame. But it's important to keep hitting them directly - as they're ultimately the vendor who sold you the good - and the choice of delivery company is their responsibility.
Best wishes
Jim
I've seen some pretty horrible scams in my day, as I used to work for a telephone relay company (which was intended for helping the deaf and hard of hearing, but abused by Nigerian/Ghana-rean? scammers because it was anonymous and free)
I wouldn't under-estimate the importance of them specifically trying to get their hands on a kindle, like you mentioned, since it comes pre-registered to your account, I'm guessing 9/10 kindles they get are not deactivated as quickly as yours and that may be just what these people are after.
Sorry to hear about your experience, but thank you for taking time to spread the word.
Two-for-one: Amazon.com’s Socially Engineered Replacement Order Scam
http://www.htmlist.com/rants/two-for-one-amazon-coms-socially-engineered-replacement-order-scam/
http://gizmodo.com/5969981/two+for+one-amazons-socially-engineered-replacement-order-scam
So, a smuggled Kindle here would give the guy that much money. The guy talking to the Amazon representative might not be the BOSS, the boss could easily get 10 people to work for him for U$100.00 a day. If in 10 days, 10 Kindles are shipped per scammer then you get 1,000 Kindles, which amount to nothing less than U$275.000 if selled in Brazil, for example.
This will cost the BOSS 100 x 10 x 10 = U$10,000.00
You can see now that there's a HUGE profit to do on this kind of scam.
http://socialengineered.net/index.php
All that work for a B/W Kindle...
http://www.consumer.ftc.gov/articles/0290-repairing-your-credit-after-identity-theft
In addition to that, this story demonstrates the downside of being famous. Sorry Scott, but you are famous :)
If I understand correctly, they didn't paid for it. It is already a benefit by itself. And even more, if you consider the fact that Kindle is much more expensive outside US. Add the fact that receiving guy may earn $10/day - then it is a bargain. If they live in a country without network coverage, then Amazon wouldn't be able to brick it remotely and they are safe.
@Kevin - Thanks for that link. I had a friend who had the same problem with a power company with someone trying to establish residence in his name and they refused to send him the information. I wish I had had the link then.
Two-for-one: Amazon.com’s Socially Engineered Replacement Order Scam
A couple of months down the line and I had to pop into the police station to sign my statement. The detective showed me a transcript of the call this guy made. He was asked the standard security questions (mothers maiden name, special place etc..) and got them all wrong. In fact the only thing he knew about me was the name on the card he had stolen. The guy handling the call said to him "I'm sorry sir but you have incorrectly answered all of the security questions. For future reference, your mothers maiden name is XXXXXX, your special place is XXXXXX and your telephone banking password is XXXXXX".
So not only did HSBC allow some random guy access to my bank account despite the fact that he failed security, but they also proceeded to tell him the answers to some pretty standard authorisation questions that he could have used against me for other accounts with different organisations!
Thank you for sharing this story. I encountered something like that in the past. I happened to find out the hacker used "who is" to lookup my domain address and got my address. I paid additional fees, not to disclose the address info from my domain registration.
Thanks
Baski
Until they're fined tens (or hundreds) of thousands of times the value of the breach, security will never improve.
That's not hyperbole, either. Security at these companies has not improved one single iota since the beginning of time, let alone the beginning of the Internet. It is, in fact, substantially EASIER to use social engineering to access a company now, given that many call centres are outsourced to external agencies in third-world countries with no data protection laws. There's a massive disincentive to providing extra security - it costs a little more to provide security, but it costs you quite literally nothing to NOT secure your customers' information.
What are the chances that anyone here, Scott of otherwise, is going to stop using their Kindle now that they know Amazon provides the same level of security as posting your bank information at a local cafe?
I particularly like how you broke open the whole scam and were able to connect the dots to the forwarder.
It is pretty clear how amazon.com could tighten up some procedures and also explain to calling customers that this is to prevent someone from impersonating them.
@Chris. It seems that banks and others should not reveal security-question answers to their support personel. They should have to type in the offered answers and get yay/nay responses the same as if one of us does it in our own account to initiate a password recovery. This whole notion of security questions being another factor is something that needs to be stamped out.
I have a worse one though. A financial institution that has too much of my money will allow recovery of user ids from passwords and vice versa. (They require that both be secret.) If you have "lost" both, they will postal mail both of them to the address of record. They cannot change the address, fortunately, but it does mean that the ID and password are not under one-way protection. Sheesh.
Thank you for sharing Scott.
- The rep did a security check asking for your address and email address. It seems they considered anything after that as a valid authorization including getting UPS to redirect shipping.
- I am not sure it's OK for them to send chat logs with sensitive information if these chats are done without logging in so do do they know it's actually you? Anyone can chat with them impersonating anyone. OK.. they asked you the security question. They also sent you the logs to your email address but didn't trust the phone call.
- I don't know of any ecommerce site that raises a red flag if I logged in from an ip address different than one I used before. All they care about is I am able to log in successfully. Anyone can be shopping from a public computer. It seems only banks go that far.
- How does Amazon remotely deactivate a Kindle? I have a non 3G Kindle Paperwhite and was able to put pdf's on it using the USB cable without enabling WIFI or registering it, effectively keeping Amazon off of it? and what does deactivating mean exactly? Bricking it? Unable to connect? Unable to put anything on it? Can't be rooted and bypass the deactivation?
The recommendations you identify are (or should be) common sense for large corporations interested in protecting themselves and their customers from fraud. How much did it cost Amazon to deal with this incident (in terms of people's time, shipping costs, etc) not to mention the erosion of confidence this creates for their brand?
I would also suggest a two-factor model for verifying identity in anonymous interactions (like phone or chat). It's entirely possible for companies to use their existing infrastructure to verify customer identity. Google (and others) already use SMS and online-login to verify customers inquiring about their account. And they use phone/SMS as a recovery model for lost passwords. It wouldn't hurt to also consider introducing pass phrases (similar but separate from your account name/password) that could be used to verify identity when on the phone.
None of these things are rocket science, and should be implemented by all companies that manage and interact with customers and their data.
Much of what you have suggested that the CSRs should have done, personally, strikes me as impractical.
CSRs are highly alienated low-wage workers who handle many hundreds of interactions per week, often with people who don't listen, don't understand what they're doing, and may try to manipulate the system for totally mundane reasons having nothing to do with fraud. They are constantly being pressured to keep handle times low and CSATs up. They work through a long chain of principal-agent relationships which make it extremely difficult to incentivize them to do anything that isn't easy to measure.
The base rate for fraud is probably low enough that *even if* you could realistically get CSRs to consistently and competently sniff out suspicious behaviour, most suspicious behaviour would turn out to be totally harmless. CSRs would see two dozen false alarms before they ever handled a fraud call. In effect you'd be training your CSRs to believe that actually exercising a nose for sneaky behavior == complicating your interactions and lowering your stats just because someone in some faraway office is needlessly paranoid.
When I worked as a CSR for (a firm that contracted with) a major US credit card issuer, it was frequently obvious that people were calling in on their spouse's account, to which they had no legal claim. We were specifically forbidden from calling this out. If we called it out anyway and refused to service the call they could just call back.
Sometimes a woman, clearly already irritated and in a hurry, would call in the account. There would be very recent call notes saying things like "wife tried to access husband's account, but not listed." During the authentication phase she would slow down, over-enunciate, affect confidence while sounding clearly nervous, and say things like "My name is Mr. Brockland Smith and my SSN is xxx-xxx-xxxx."
It was the right name and the right SSN.
We would handle the call.
I actually had a similar issue with an Xbox Live account that was luckily attached to my primary email. Someone bought points and bought Assassin's Creed (one of the non-numeric releases). Support guy was top notch on getting it handled.
Well maybe if I could order those things right from their companies... Mostly the mail taxes are higher, not cheaper if I use those, but mostly it's the only way, how to get those things.
Have a nice day Radko R.
I like your suggestions for reducing fraud. Frankly large consumer focused companies should be held responsible for ensuring that fraud doesn't happen to their customers due to their own security failures.
The only suggestion I am concerned about is the extra checks for mail forwarders. As a person who actually lives outside of the US I can say that many American companies forget that an entire world actually exists outside of the borders of America. Often times the only way to get access to certain goods is to use these mail forwarders (at often significant extra cost to myself). Even with these extra costs some goods can be hundreds or even thousands of dollars lower than the local option (when a local option even exists).
American companies response to extra work has consistenly been simple bans. Which would eliminate the option of getting goods forwarded through these services for non-Americans (and since anyone can technically create a mail forwarder its impossible to actually track them [it requires just a legal contract to be filed with the US Post Office and poof]).
There is also no way customer rep could know if the delivery address is a forwarding address. Unless he just happens to know that. It is a long shot.
Spotting odd behavior is also very very difficult, you should listen to actual honest calls, they are sometimes really weird. Asking not to sen emails, well that is odd but not more so than stuff these reps hear every day. Maybe amazon sends 54 emails, questionnaires etc and this guy is on mobile connection and has to pay for each email downloaded or something like that.
I didn't find on this article about how the actual order happened, was it done on live chat? If it was, how was it done? At that point they should have requested password or to log on, if they didn't there should be good reason for it. After that, I really don't see Amazon have done anything wrong. Sometimes things can't be done by the book, you have to bend rules. For exampl something that happened to me some time ago: I lost my driving license, legally I could not get a replacement driving license because I live abroad and law (in my home country) says "application must be done at your current home town you are registered to" - well that was impossible because I lived abroad (and my original home country doesn't have police stations abroad). So if the police kindly had bent a rules a bit I had been happy. I bet most Amazon customers are happy because occassionally Amazon bends the rules a bit. Usually there isn't harm done, it is just good customer service. Sometimes bad things happen, but it is the whole picture that counts.
So actually there's another "breach" in their system: they did send you a chat transcript from an anonymous chat session.
While Amazon doesn't enforce real names in their reviews (unlike, e.g. Google Places), many users undoubtedly opt to use their real names in reviews.
Together with the 'verified buyer' tag, a scammer will be able to (a) identify what product a person bought along with any other information disclosed in the review (including potential customer service issues when people mention they already returned a unit once, etc.).
This provides effective filtering for likely targets, right on Amazon's website.
Corporate sponsored identity theft, again using information in the public domain to access peoples voicemail - even that of a murdered teenager ! Disgusting.
That ups the cost of executing a successful scam to gaining access to the email account or adding an email address to the customers account, which the bad guys were not able to do in this case.
I used to work a lot with manual fraud detection, and it always amazed me how easy it was to identify most of the attempts by simply paying attention to patterns in grammar and casing.
Google the name of the person you're ripping off before you start. You may not know who "Scott Hanselman" is but if it looks like the rest of the internet does, you might want to choose another target.
That's how this stuff makes me feel.
Vulnerable and *angry*.
In the previous instance, someone's macs/iphones/ipads were remote wiped which was definitely more troublesome than a onetime loss, but it goes to show Amazon is playing fast and loose here.
The amazing service that Scott is raving about is working to the detriment also and is actually the problem.
They are trying to give an amazing service without verifying properly to whom they are providing the service.
I guess the only way to stay safe is use a 'amazon only' email account that has no relationship to anything else you do online!
How many hours would you estimate you ended up spending on this?
Scott, so sorry you went through this Kindle-chat- fraud-mess...
Thankful you shared how it happened and are making strong suggestions that will aid Amazon in remedying this.
All the best,
@CorettaJackson
But how do you know the address is a "known international logistics package distributor"? Who should be responsible for "knowing" this, Amazon or UPS? Perhaps UPS should flag it, "hey Amazon, this address is a known re-distributor, do you wish to proceed?". This way other companies who are not Amazon could avoid this fraud.
http://en.wikipedia.org/wiki/No_worries
It is commonly used here in the UK. I wouldn't have thought it was widely used in the states though.
This is the easiest and probably cheapest way to order a Kindle or Nexus 4, at least while they're new - after about 6 months on the market, resellers start stocking them and you can just buy them locally.
2 possible things to help combat this.
1. Replacements should not ship until you log in to Amazon. This is the least convenient for the customer.
2.Disable chat as a vector to redirect the shipment once a replacement has been requested. Further chat has to happen by enabling it in your account settings.
You missed that Amazon gave the phishers your phone number without even being prompted, so now they have that information about you as well.
Then Amazon Support asks for a phone number and it doesn't match the one in the shipping information!
The good thing is that in addition to helping them stop the fraud, you're also exposing huge flaws in their system to a large audience. If you're going to be a detective for the retailer, you might as well act as a reporter for the consumer. Things only change when those who are responsible are held responsible and face consequences.
If someone is using MY ACCOUNT to order things using MY MONEY, then I don't care if they're the Pope or the President, they have given up ALL of their rights, as far as I'm concerned.
People are a bit too over-eager to protect a clearly proven criminal.
Now, you can say that the solution is that any product that launches in the US should be available worldwide within a few days, but that's not always feasible.
Just my two cents.
That said they seemed to know the name, email address and home address of the target.
On the flip side Amazon customer service has helped me with a bunch of packages that UPS didn't update at all for 20-30 hours. Occasionally resulting in duplicate delivery, that I return.
The company then legally has to provide this information.
Technically this information is not a conversation with Scott however that's not what Amazon seem to think therefore in Scott's defense of this - Under UK law at least he has every right to the conversation that resulted in someone who claimed to be him making a key change to his account with amazon.
I agree 100% with Scott on this, he shouldn't have to solve this type of problem because someone "socially hacked amazon reps" but in doing so at the very least amazon now owe him for his time (not that are legally obligated to provide him any compensation).
However Scott could easy raise further legal action against amazon for leaking personal information about him to a third party which could result in some heavy fines for amazon.
More so if it became a class action!
Amazon security is shocking and it wouldn't take a lot for them to put some basic measures in place to prevent this type of thing ... any smaller company would be publicly shredded by now!
I'm reminded of the Mat Honan incident. A new credit card was added to his account and then social engineers immediately called back using that same credit card for verification.
Amazon needs to improve its fraud detection systems (if they have them). They could take some hints from the credit card industry.
I also think it ridiculous that people don't think Scott shouldn't have received the chat logs. The person was pretending to be him after all.
Even though this was Scott's account he was doing Amazon a favor doing an investigation that Amazon itself should have been doing. Scott's account wasn't going to be charged. But Amazon would be losing money.
I know for a fact that Amazon has fraud investigators. Now I'm wondering what they do.
After calling Amazon, I understood that somebody from Indonesia digitally ordered bunch of MP3s through cloudplayer and Amazon put a hold on my account.
With Amazon Payments team help, I was not only able to get back my account but also got those transactions reverted.
After reading Scott's blog, it looks like there is some serious hacking going on in Indonesia..
like http://enhanced-identity-theft-protection.com/irs-identity-theft-form-can-provide-you-better-protection/ give an ip adress when a user came to site and enter his login.
Comments are closed.

As you mentioned... Think about the stuff one could buy with a preregistered kindle with One Click Ordering turned on...