Phishing...for EVIL!
Just happened to get this in my evening email. It's obviously a standard Phishing scam. If you look at the source (as I usually do to most suspicious looking HTML email) you can see that the links point to urls like: http://www.scgi3-ebay-saw-cgi-ebayisapi-dll-registerenterinfo.xx.com. Note that the first part of the URL is really just a very long subdomain, pointing to the evil person's actual domain (xx.com in this example.) Additionally that domain's WHOIS record points to a fake person, blah blah. Their domain points to freeservers.com which does roaming DNS which points to a webserver on their personal computer lord knows where. When you submit your Credit Card it goes via an unencrypted Form POST right to their computer. Evil!
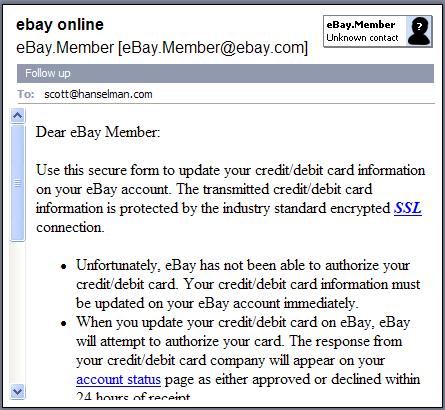
What I found particularly interesting was what is revealed in this screen shot from my Outlook. What's interesting...do you see it?
The scrollbar is on the LEFT. Further digging shows that the HTML body for this message was created with FrontPage and they've explicitly set the encoding to Windows-1252 and attempted to switch all the tags to dir="ltr." However, Microsoft FrontPage when running in Right-To-Left Locales (Arabic, Hebrew, etc.) will default the HTML root tag as <html dir="rtl">. As every OTHER tag in the document is explicitly marked dir="ltr" the document elements look OK, but since they missed the root tag, Outlook moves the scrollbar to the left, thus making their chicanery even more obvious. Additionally it makes me wonder what country these folks are phishing from.
About Scott
Scott Hanselman is a former professor, former Chief Architect in finance, now speaker, consultant, father, diabetic, and Microsoft employee. He is a failed stand-up comic, a cornrower, and a book author.
About Newsletter
Comments are closed.